All Articles - Page 3
Your Personal AI Assistant: Details about Microsoft Copilot for Office 365
[vc_row][vc_column][vc_column_text] Your Personal AI Assistant: Details about Microsoft Copilot for Office 365 Imagine a tool that could anticipate your needs,...

Cybersecurity Alert – What is Quishing?
[vc_row][vc_column][vc_column_text] Cybersecurity Alert – What is Quishing? Quishing is a relatively new type of cybersecurity risk that has emerged in recent...

Cybersecurity is an Ongoing Process, Not a One-and-Done Introduction
[vc_row][vc_column][vc_column_text] Cybersecurity Is An Ongoing Process, Not a One-and-Done Introduction In today’s digital age, where data breaches and...

Enhancing Your IT Services with a Cybersecurity-Centric Managed Services Provider
[vc_row][vc_column][vc_column_text] Enhancing Your IT Services with a Cybersecurity-Centric Managed Services Provider Introduction Businesses rely heavily on...

Why You Should Conduct a Cybersecurity Audit
[vc_row][vc_column][vc_column_text] Why You Should Conduct a Cybersecurity Audit In a world where businesses and individuals alike rely on technology for...

The Value of Proactive Cybersecurity Insurance Audits
[vc_row][vc_column][vc_column_text] The Value of Proactive Cybersecurity Insurance Audits Introduction In an age where digital landscapes are expanding at an...

What to Expect From Your IT Support Company: A Comprehensive Guide
[vc_row][vc_column][vc_column_text] What to Expect From Your IT Support Company: A Comprehensive Guide Introduction In our technology-driven era, a dependable...

Backup Is All About Restoration: What 35 Years of Disaster Recovery Taught Us
Backup means nothing if you can’t restore. Learn how Eaton’s backup and disaster recovery services protect Bay Area businesses with tested, proven recovery...

The 20 Most Used Acronyms in IT
[vc_row][vc_column][vc_column_text]The world of IT is full of acronyms. Some of them are well-known, while others are more obscure. But no matter how familiar...

Securing Your Data with Role-based Network Access (RBAC)
[vc_row][vc_column][vc_column_text]Role-based access control (RBAC) is a method of restricting access to network resources based on a user’s role within an...

Ditch Your Mouse… Keyboard Shortcuts Are Faster!
[vc_row][vc_column][vc_column_text]Do you spend a lot of time clicking around on your computer? If so, you’re not alone. But did you know that you could be...
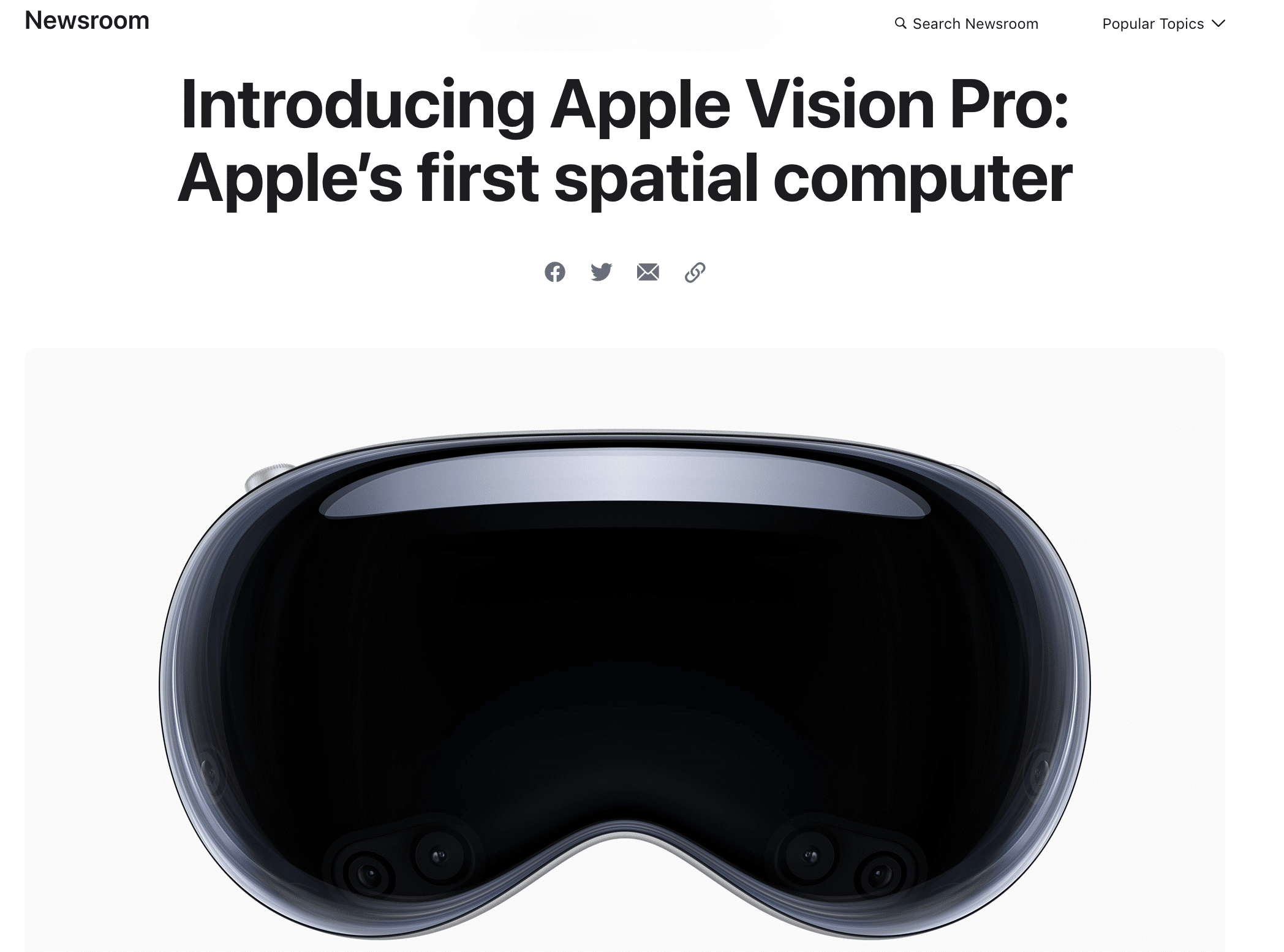
Apple Vision Pro: A Powerful Tool for Businesses of All sizes
[vc_row][vc_column][vc_empty_space][vc_single_image image=”6622″ img_size=”Full” alignment=”center”][vc_empty_space][vc_column_text] Apple Vision Pro: A...